Why attend this webinar?
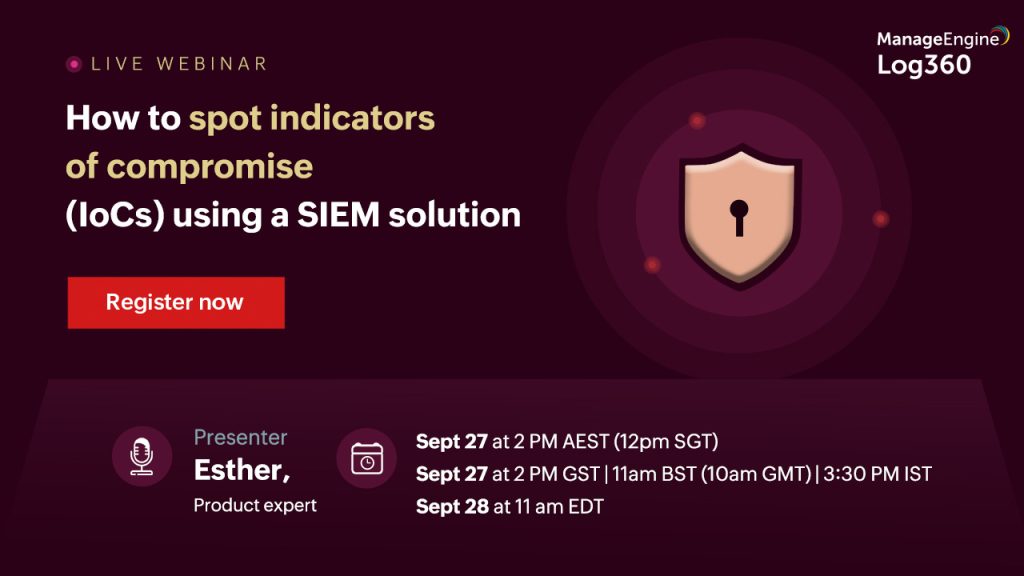
Cybersecurity professionals can use IoCs to track an attacker’s presence, understand their attack methods and detect unusual activity that could be evidence of an attack and prevent future attacks. In this webinar, we’ll delve into 6 indicators of compromise and discuss methods in which Log360, a SIEM solution, can help detect abnormal activities in your network and defend against them.
Agenda:
- What are indicators of compromise and how they work
- The difference between IoCs, IoAs and TTPs
- Hunting common IoCs
- How a SIEM solution can help detect IoCs in your network
Speaker

Product expert
ManageEngine